Outrageous Tips About How To Check Active Directory Logs

For example, on the azure active directory menu, you can open the log in the monitoring section.
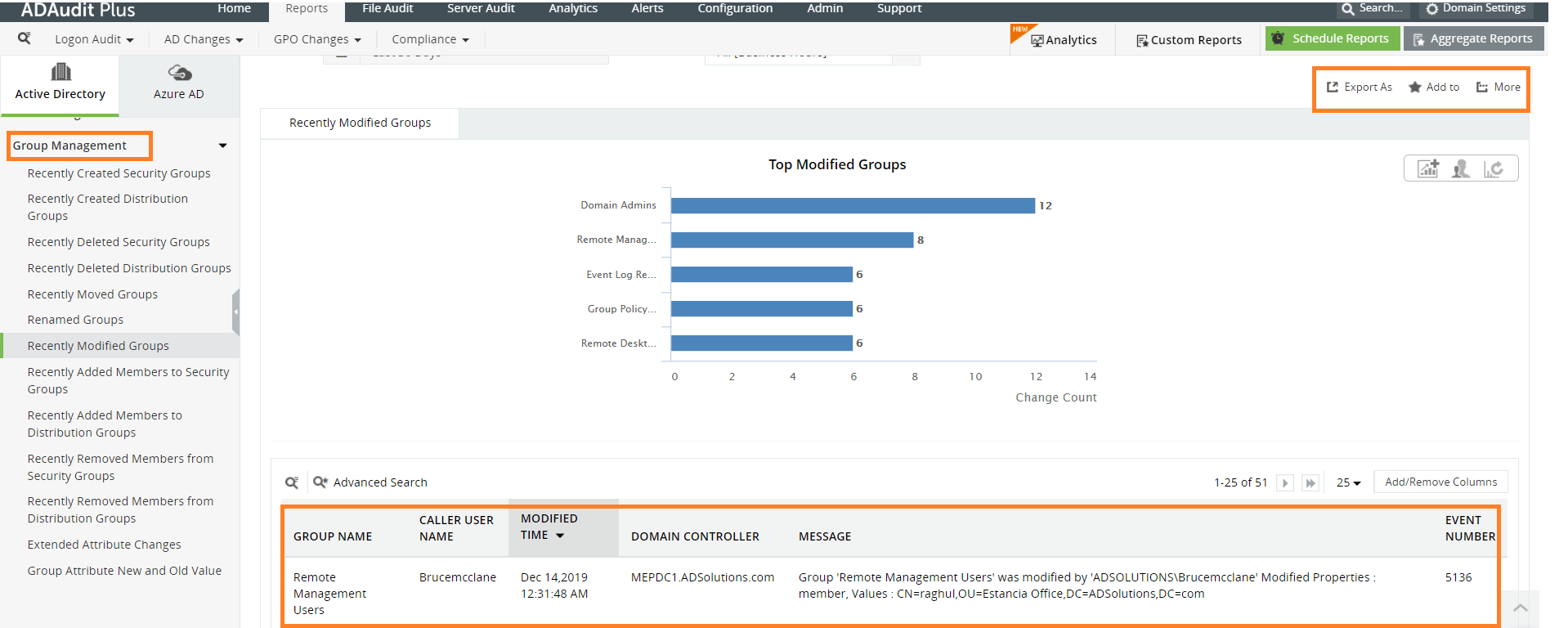
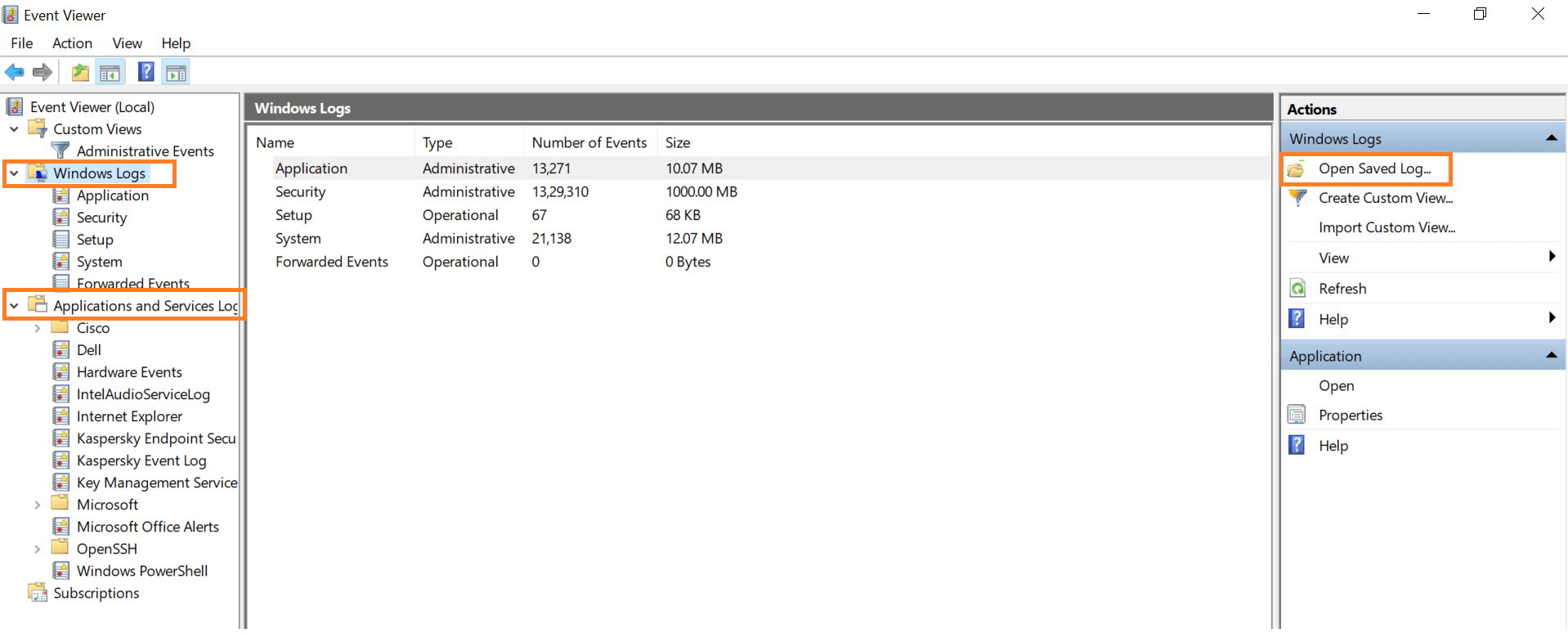
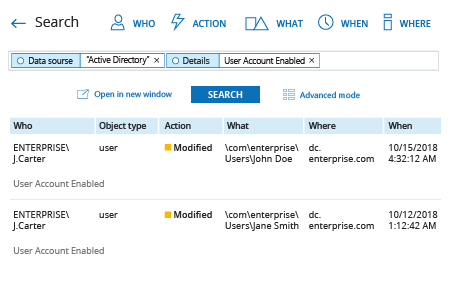
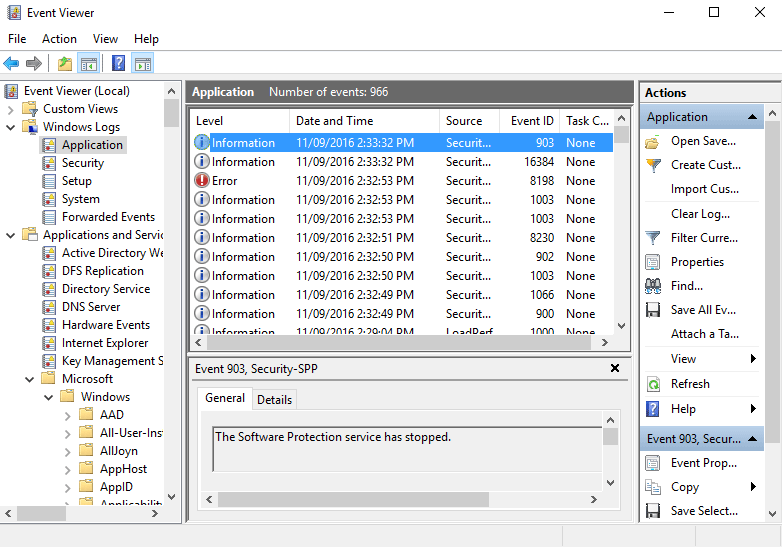
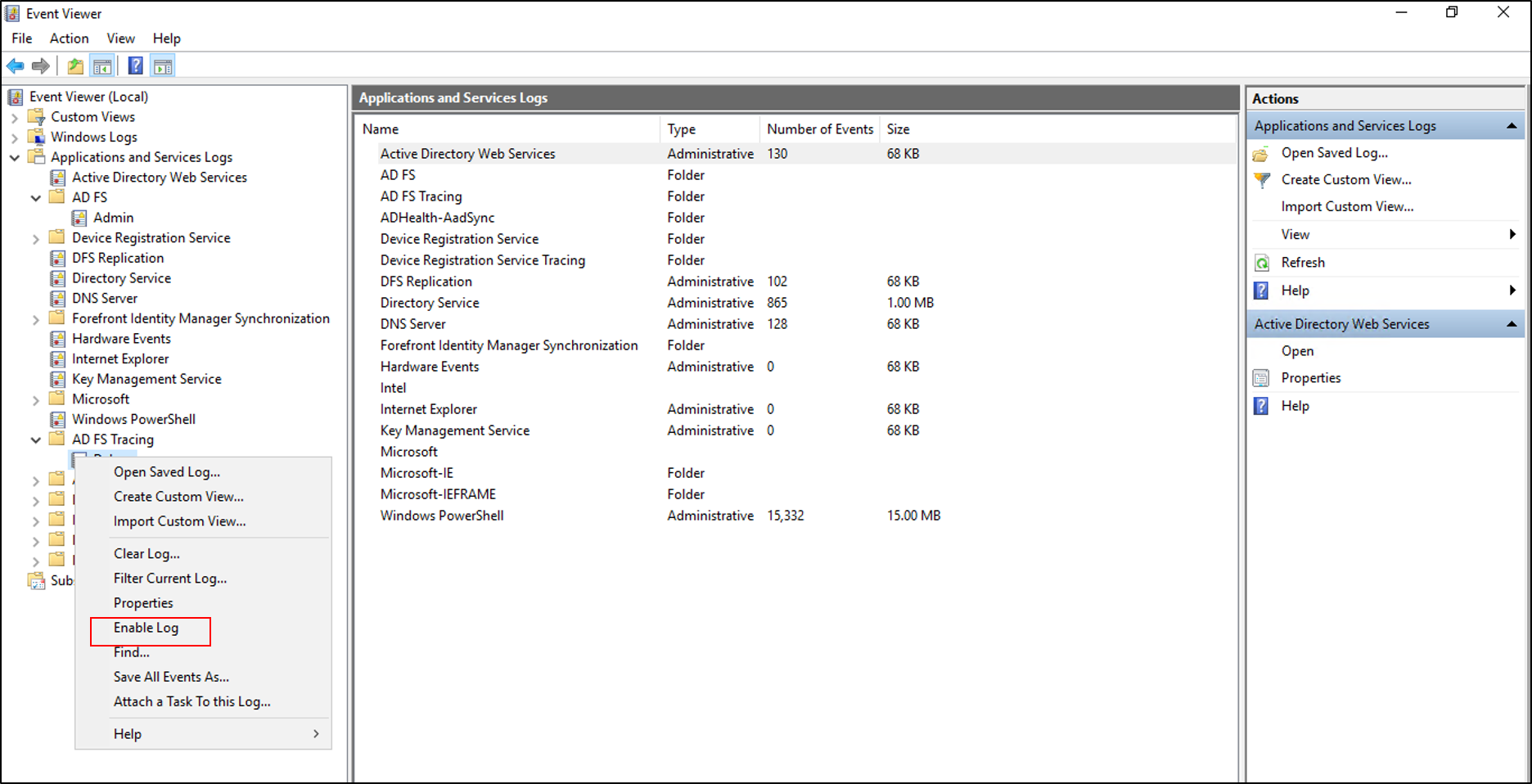
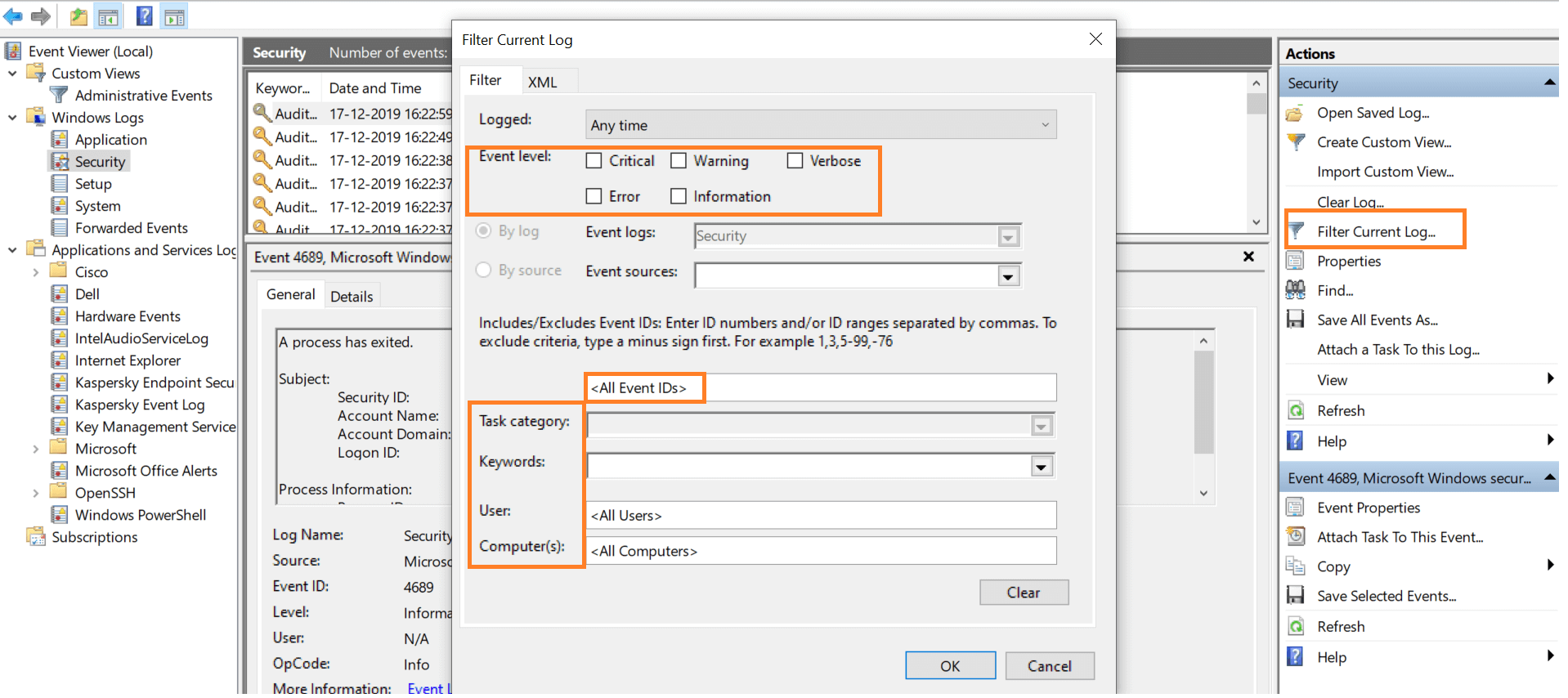
How to check active directory logs. Below we're looking for “a user account was enabled” event. Azure monitor provides a very easy way to analyze logs from azure ad, as well as other azure services and independent tools. To track user account changes in active directory, open “windows event viewer”, and go to “windows logs” “security”.
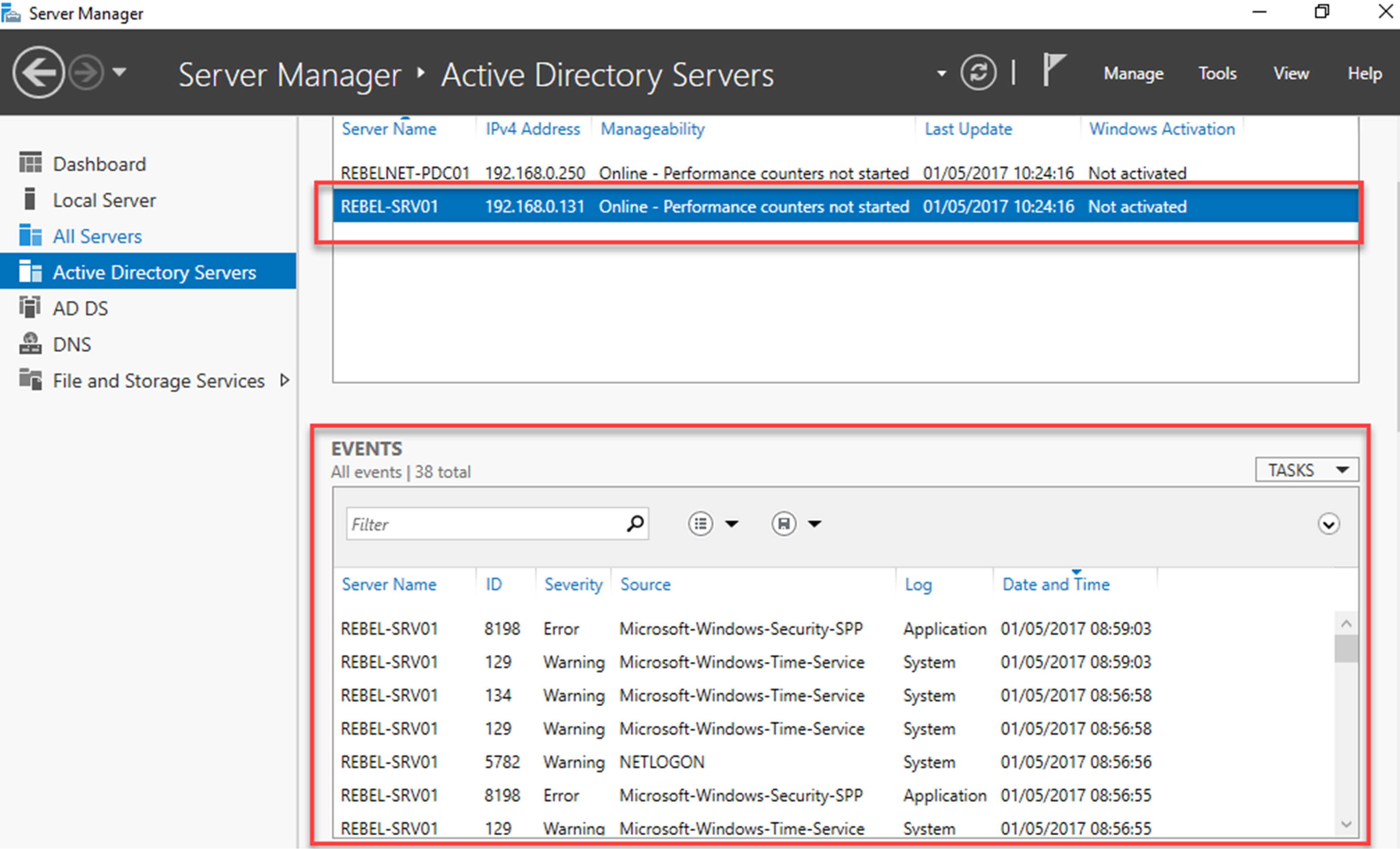
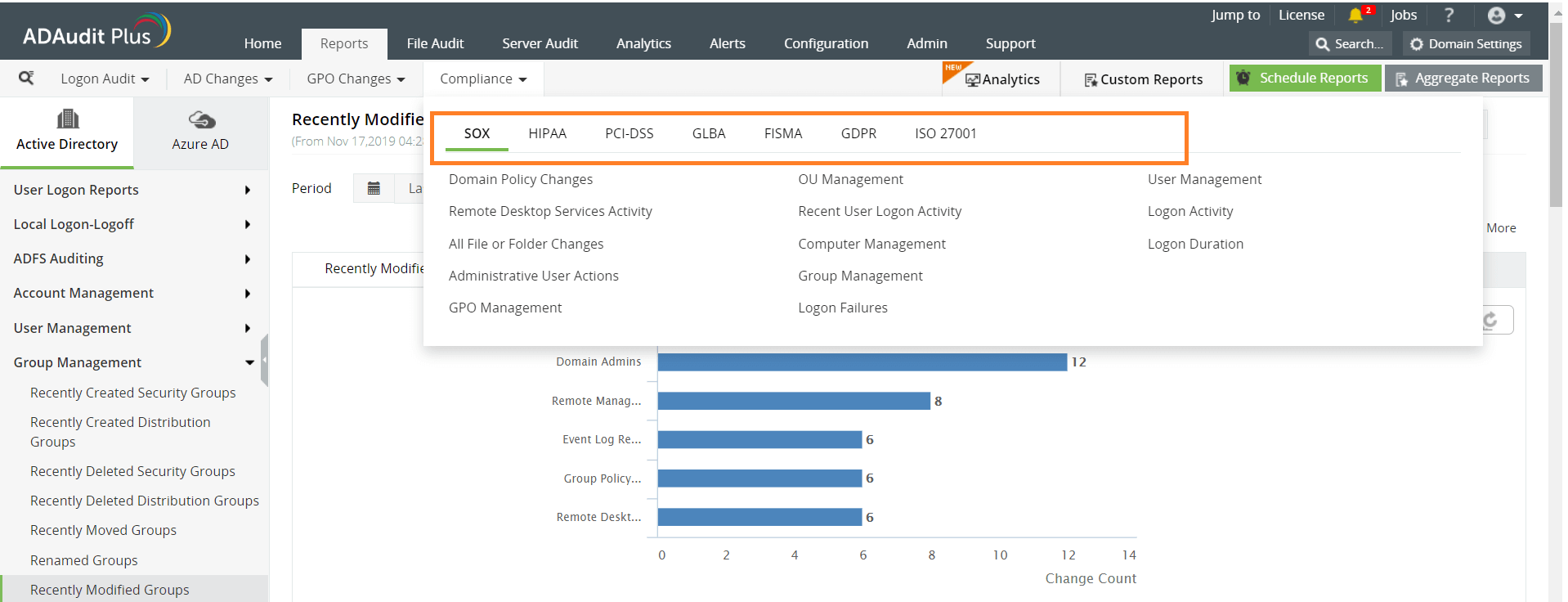
I’ll count on you to read help and examples. Use the following script to list the ad users logon information, including the computers from which they logged on by inspecting. To support you with this goal, the azure active directory portal gives you access to three activity logs:
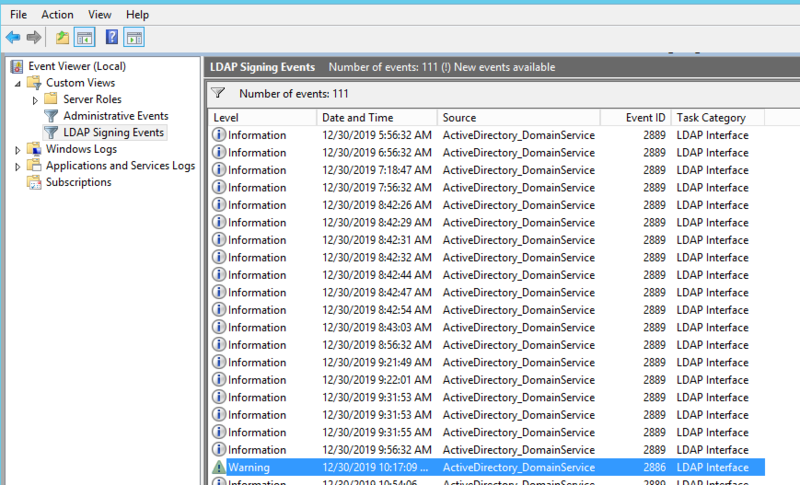
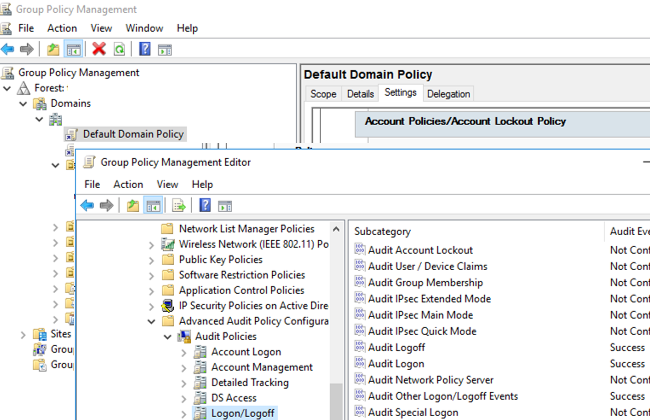
In the policy tab of audit credential validation. Click windows logs → choose the security log. Each event type in log has its own event id.
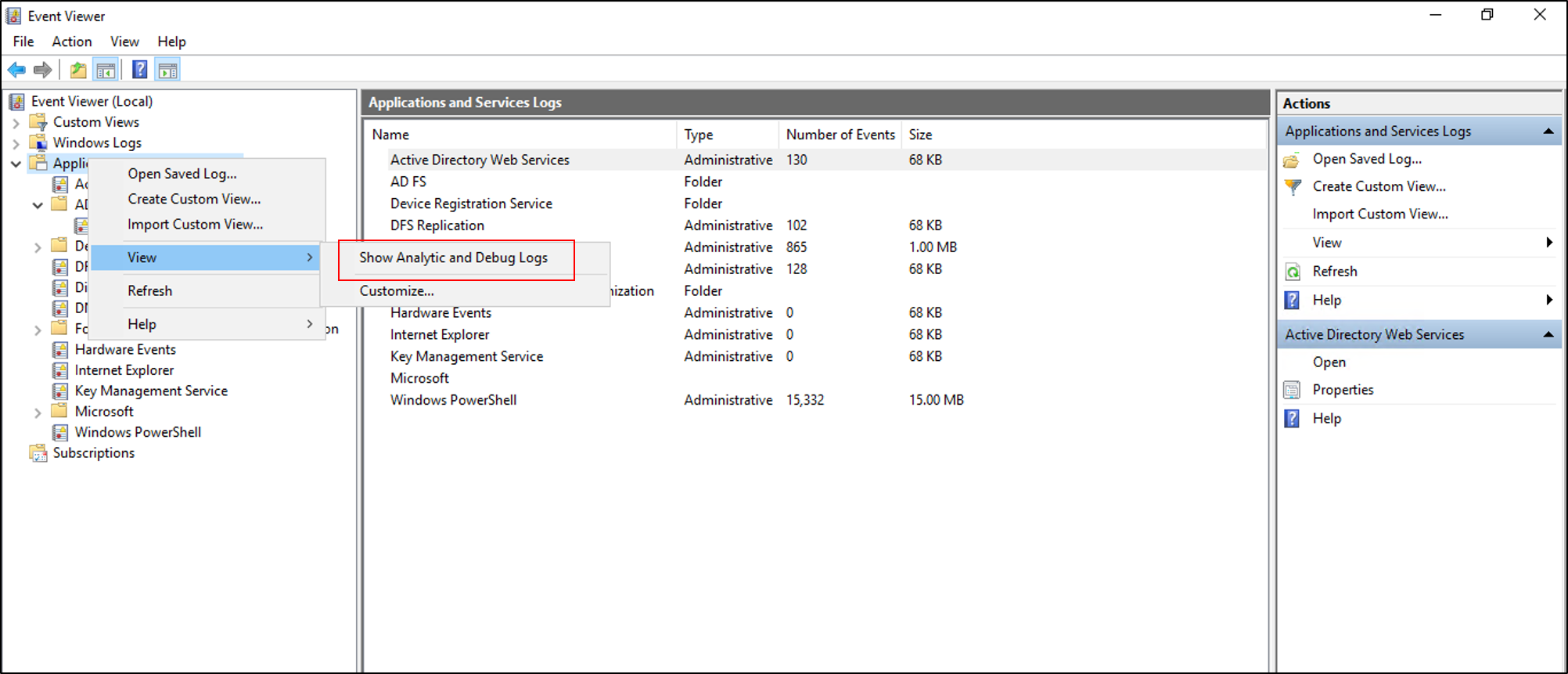
Event viewer is a console where you can view all significant activity happening on your windows device. Use the “filter current log” option in the right pane to find the. # find dc list from active directory.
Open the powershell ise → run the following script, adjusting the timeframe: It offers more querying flexibility, is a little bit faster (i think) and when you get to powershell 7 is the only tool you’ll have. Check both success and failure.
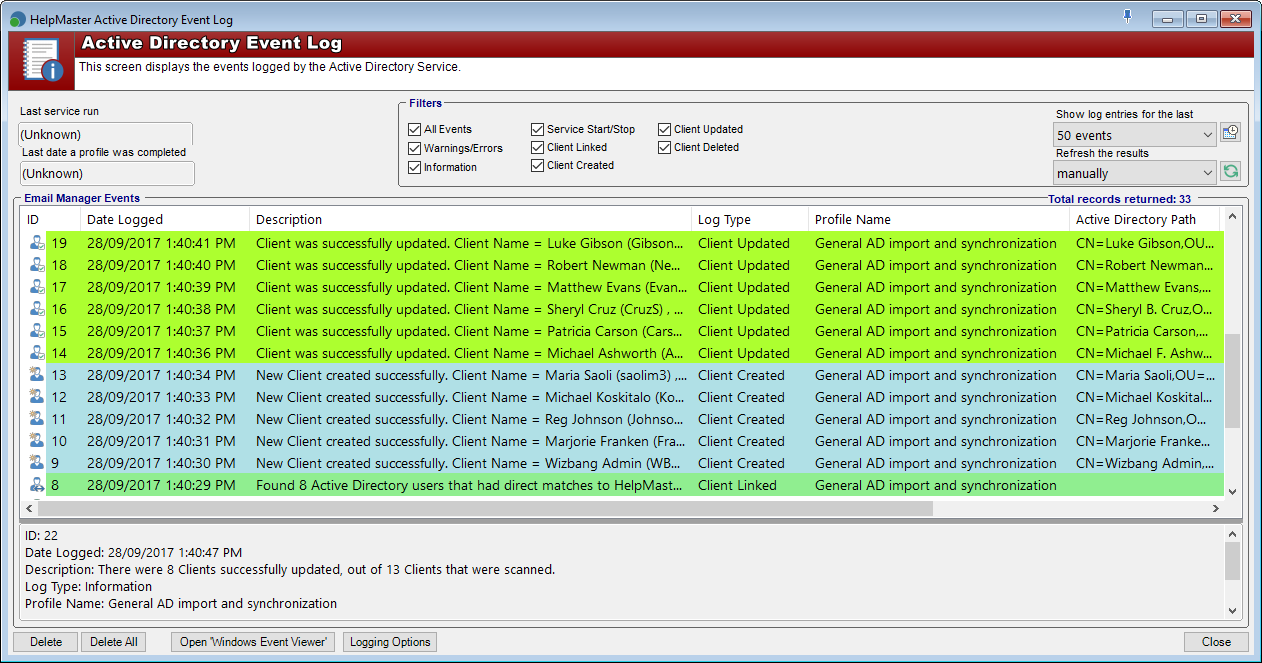
Active directory event logging tool. How to check all users' login history in active directory? For instance, event viewer provides information on.